What Are Crypto Wallets and How They Protect Your Funds
- Crypto9D
- March 3, 2026
Cryptocurrency can feel abstract and intangible. Unlike traditional money, there are no physical bills or coins to hold. Instead, cryptocurrencies exist entirely as records on a blockchain, a decentralized digital ledger. So, when someone acquires Bitcoin, Ethereum, or any other digital currency, the immediate question is:
Where does it actually reside?
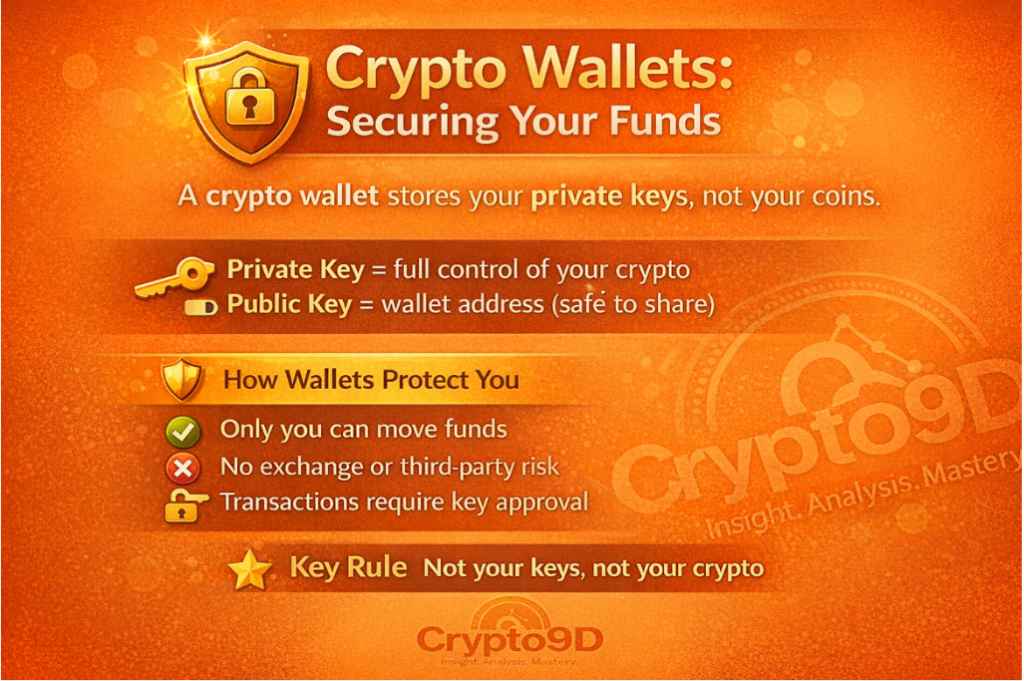
The truth is that your cryptocurrency never truly “lives” in a wallet like cash lives in a purse or a bank account. The blockchain always stores your funds. A crypto wallet acts as the interface that allows you to access and manage them. Essentially, a wallet manages your cryptographic keys, which are the codes that prove ownership of and control over specific digital assets on the blockchain.
Grasping how wallets operate and how they secure your funds is essential, especially since cryptocurrency doesn’t provide a central authority to reverse transactions or recover lost access. Unlike banks, responsibility for your assets rests entirely on you.
Understanding the asset security in the crypto market
At its core, a crypto wallet is a software application or hardware device designed to store your private keys safely. These private keys are unique cryptographic strings that grant you access to your cryptocurrency and authorize transactions on the blockchain.
When you own cryptocurrency, what you actually hold is a private key associated with a public address. This key is what proves to the network that you are the rightful owner of your assets.
To make this concept simpler:
- The blockchain functions as a global record book.
- Your public address is like an account number.
- Your private key is the secret password that allows transactions.
- Your wallet securely manages that password and lets you interact with the blockchain.
It’s important to note:
the wallet itself does not contain your cryptocurrency. Instead, it stores the keys that allow you to access and move your funds.
Public Keys vs. Private Keys
Crypto wallets operate using two main cryptographic components:
Public Key (and Address)
This is the address you can share publicly so that others can send funds to you. While anyone can send crypto to your public address, only the person with the associated private key can access or spend it.
Private Key
This is the critical piece that grants you control over your crypto. If someone gains access to your private key, they can transfer your funds, and these transactions are irreversible.
Most modern wallets also provide a seed phrase — a set of 12 to 24 words that acts as a backup for your private key. If your device is lost or damaged, you can restore access to your wallet using this phrase. However, if both your device and seed phrase are lost, your funds are gone forever. This is not a flaw, but rather a fundamental aspect of blockchain-based security.
Types of Crypto Wallets
Wallets come in various forms, each offering a trade-off between convenience and security.
1. Hardware Wallets (Cold Wallets)
Physical devices known as hardware wallets are used to store private keys offline. They connect to a computer or smartphone only when signing a transaction. Because they remain offline most of the time, they are extremely resistant to hacking.
Advantages:
- Keys never leave the device.
- Transactions are signed internally on the device.
- Immune to malware on computers or smartphones.
Ideal for: People holding large amounts of cryptocurrency or planning long-term storage.
The downside is that hardware wallets are less convenient for frequent transactions and require careful physical storage to avoid loss or theft.
2. Software Wallets (Hot Wallets)
Applications installed on your computer or mobile device are known as software wallets. They are connected to the internet, which makes them easy to access and use for daily transactions.
Advantages:
- Quick setup and access.
- Suitable for everyday spending.
- Convenient for smaller amounts.
Disadvantages:
- Vulnerable to malware if your device is compromised.
- Can be targeted by phishing attacks to steal private keys or seed phrases.
Hot wallets are best for regular use, but storing significant amounts of cryptocurrency on them is generally not recommended.
Noncustodial Wallets
Noncustodial wallets provide you a massive control over your private keys.
Pros
- Complete ownership of assets.
- Reduced counterparty risk.
- More privacy and autonomy.
Cons
- You will always lose money if you lose your seed phrase.
- You are entirely responsible for security.
- Financial autonomy, the foundational idea of cryptocurrencies, is embodied in noncustodial wallets.
How Crypto Wallets Protect Your Funds
Crypto wallets employ strong cryptography to safeguard your assets. Here’s how:
1. Digital Signatures
When a transaction is initiated, your wallet generates a digital signature using your private key. The blockchain network then verifies the signature. If it matches your public address, the transaction proceeds.
Without a valid private key, no transaction can be approved.
2. Encryption
Wallets typically encrypt private keys on your device. Even if your phone or computer is stolen, unauthorized access is prevented without the encryption password or biometric verification.
3. Offline Storage (Cold Security)
Hardware wallets, or cold storage, keep keys offline, removing exposure to online attacks. This method is highly recommended for securing substantial holdings.
4. Seed Phrase Backups
Seed phrases allow users to recover wallets if devices are lost or damaged. However, if someone else discovers your seed phrase, they can access your funds from anywhere. Therefore, secure offline storage of these phrases is essential.
Common Risks for Wallet Users
Even though blockchains themselves are secure, wallets introduce certain risks:
Phishing Attacks
Scammers trick users into revealing seed phrases via fake websites or emails. Legitimate platforms will never request your seed phrase.
Malware
Malicious software can replace wallet addresses or capture sensitive information.
Social Engineering
Fraudsters may impersonate customer support or investment advisors.
User Errors
Sending funds to the wrong address or network is permanent since crypto transactions are irreversible.
Best Practices for Securing Wallets
To protect your assets:
- Store seed phrases offline; avoid screenshots or cloud storage.
- Use hardware wallets for long-term holdings.
- Enable two-factor authentication on custodial accounts.
- Confirm wallet addresses before sending transactions.
- Test with small amounts before large transfers.
- Keep devices updated and secure.
- Never share seed phrases or private keys.
Maintaining security is not complicated but requires careful attention.
Crypto Wallets in the Financial Ecosystem
Crypto wallets shift control from centralized institutions to individuals. In traditional banking, banks:
- Maintain account records.
- Can freeze funds.
- Can reverse transactions.
With crypto:
- The blockchain maintains a decentralized ledger.
- Wallet owners control access.
- Transactions are irreversible once confirmed.
This model empowers individuals but also requires personal responsibility. In areas with unstable economies or limited banking access, wallets provide unparalleled financial autonomy.
Are Crypto Wallets Safe?
Technically, crypto wallets are extremely secure. The underlying cryptography of Bitcoin, Ethereum, and other cryptocurrencies has proven robust against attacks.
Most losses occur not because of blockchain vulnerabilities but because:
- Users share seed phrases.
- Devices are compromised.
- Funds are left on exchanges that fail.
- Basic security practices are neglected.
When used correctly, crypto wallets are highly reliable.
User Case
Practical Example:
Ali wants to buy some Bitcoin for long-term investment. He decides to use a hardware wallet to keep his crypto safe. He sets up the wallet, writes down the 12-word seed phrase, and stores it offline in a secure safe.
When Ali wants to send Bitcoin to a friend, he connects the hardware wallet to his computer, signs the transaction on the device itself, and the blockchain verifies it. Even if his computer gets a virus, the funds remain safe because the private keys never leave the hardware wallet.
This shows how a crypto wallet not only allows Ali to access and use his crypto but also protects his funds from online threats.
Conclusion
A crypto wallet is far more than software or a device — it’s your key to digital ownership. It manages your private keys, enabling secure interactions with the blockchain without reliance on banks.
The essential takeaway: your private key is everything. Protect it, back it up, and never share it. With careful usage, crypto wallets provide one of the most secure, independent, and empowering financial tools ever created.
Secure your digital assets with Crypto9D — the smart, easy-to-use wallet that keeps your private keys safe while giving you complete control over your funds. Don’t leave your crypto at risk.
Related Articles:
Top 10 Promising AI, DePIN & RWA Projects – with High Growth Potential for 2026
- Master the art of crypto scalping in 2026 – See how crypto scalping works
What Is Copy Trading? – How It Works
What Is Bitcoin and How Was It Created? – Bitcoin is the world’s first decentralized digital currency
How Digital Assets Operate – Understanding the Systems Behind Digital Value
Liquidity in Crypto Trading – What It Means and Why It Matters
What Are ETFs – and How Are They Transforming the Way People Invest?
Top 5 Safest Crypto Exchanges – for Beginners:2026 Comprehensive Guide
Want deeper crypto insights that actually matter?
Join Crypto9D and stay informed, prepared, and ahead of the market.
External Resources
For deeper learning on cryptocurrency wallets and security, check out these trusted resources:

